![]() In the early days of networking splitting a network into segments required a router.
In the early days of networking splitting a network into segments required a router.
VLANS or Virtual LANS is a technology that allows you to split a home network into segments using low cost switches.
Generally a switch will send broadcast traffic to all connected ports, and will allow devices connected on any port to communicate with any other device.
VLANS were created in order to reduce the amount of broadcast traffic on a network.
However on home networks they are used mainly to improve network security.
How Do VLANs Work
If we consider a switch with 8 ports as shown in the schematic below.
A broadcast sent from a device attached to any port will be sent to all ports.
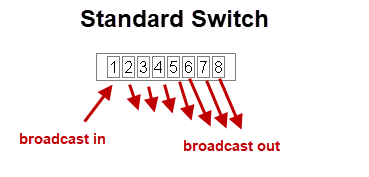
In addition any device attached to any port can communicate with any other device attached to any port.
This becomes problematic when you have untrusted devices with access to your network or as in the case of home automation you have IOT devices that are possibly vulnerable to attack.
However with a VLAN capable switch it is possible to restrict broadcasts and to control which devices can communicate with each other.
This makes it possible to design a more secure home network.
If we now take out 8 port switch and split it into two VLANs which we call VLAN1 and VLAN2 as shown below.
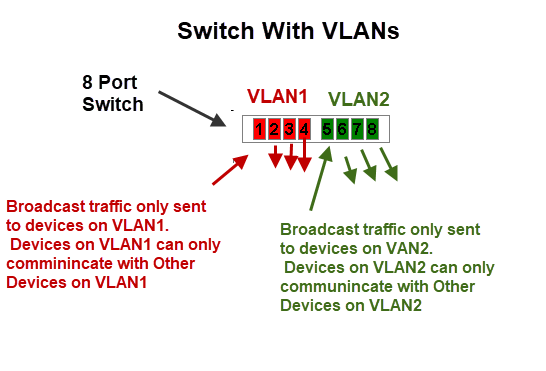
In this configuration we effectively have created two independent networks.
Devices connected to VLAN1 cannot communicate with devices that are connected to VLAN2 and vice versa.
To accomplish this the switch maintains tables of VLANs and MAC addresses.
Just as in normal switch operation it knows the MAC address of the device connected to each port and in VLAN mode it knows to only send the packet to a device with a MAC address on the same VLAN.
VLAN Uses on A Home Network
On Home networks the main use is for security where you want to isolate certain devices from each other.
You will need to choose which devices to use to implement your VLAN and the VLAN mode to use.
VLANs are supported on routers (not all) and on network switches.
On routers the VLANS have different IP subnets.
VLAN Modes
Most devices will support multiple VLAN modes.
The TP link smart switch(TL-SG105E) supports three modes:
- MTU VLAN (Multi-Tenant Unit VLAN)
- Port Based VLAN
- 802.1Q VLAN
which mode you need to use will depend on your network requirements.
MTU VLAN (Multi-Tenant Unit VLAN)
This uses a shared uplink port that is normally connected to the Internet.
The other ports can send and receive data on the uplink port but not between each other as shown in the schematic below:
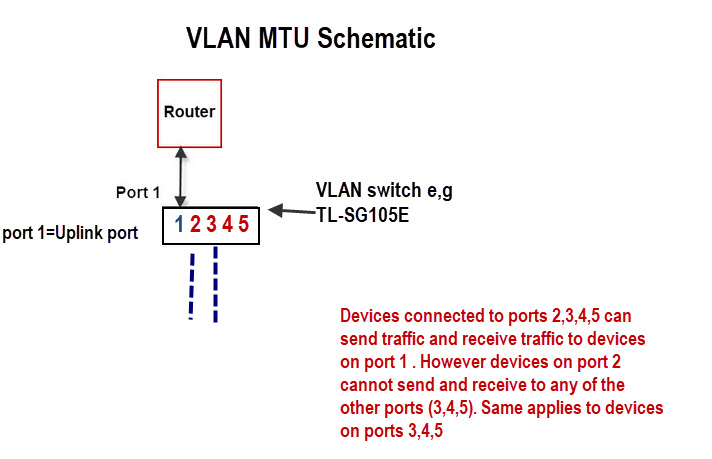
This is very easy to configure as all you really need to do is choose the uplink port (shared port) and enable it.
For example it can be used to:
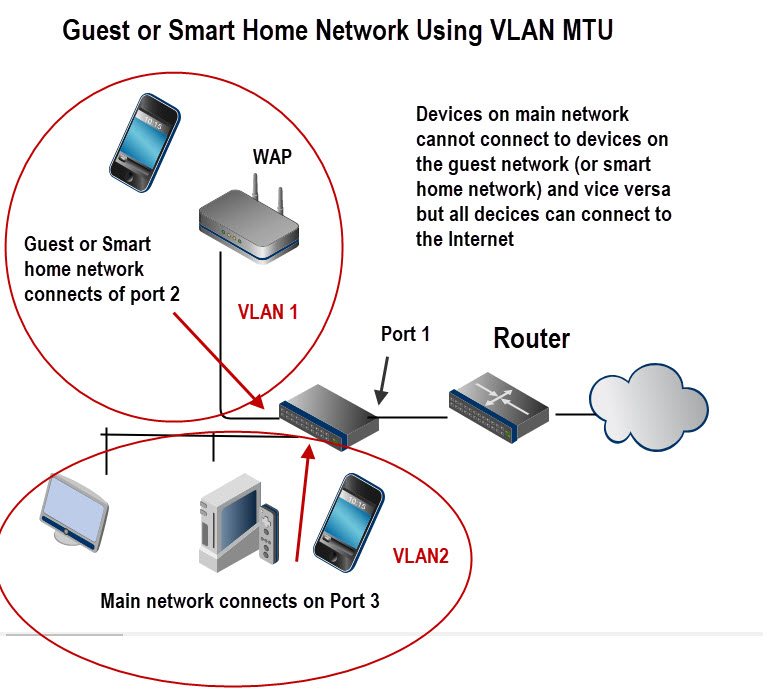
- Create an isolated guest network.
- create an Isolated smart home network.
The schematic below shows the basic layout:
Port Based VLANS
In this mode a VLAN can consist of several ports but a port can only exist on one VLAN.
It is used when you want to create an isolated network.
A possible configuration is shown in the schematic below:
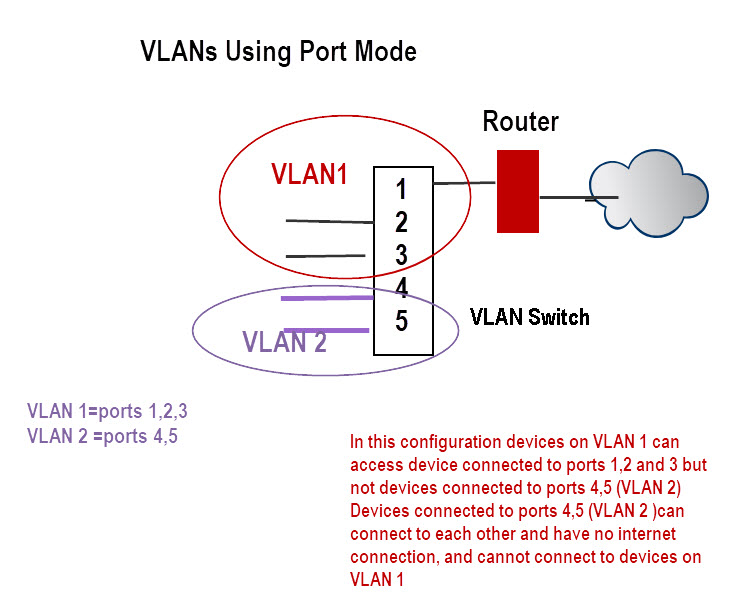
In this configuration devices on VLAN 1 can access device connected to ports 1,2 and 3 but not devices connected to ports 4,5 (VLAN 2).
Devices connected to ports 4,5 (VLAN 2 ) can connect to each other and have no internet connection, and cannot connect to devices on VLAN 1
802.1Q VLAN
This is the most flexible mode but also the most difficult one to configure.
The IEEE 802.1Q protocol defines a new format for the Ethernet data frame by inserting a VLAN tag in the data frame data frame as shown in the schematic below:
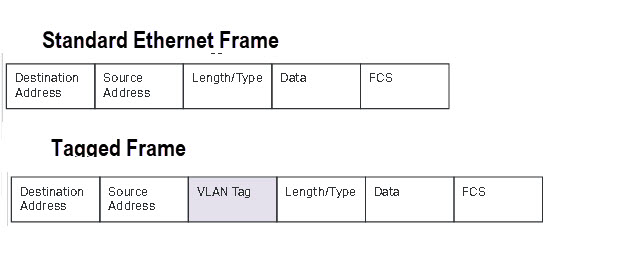
Tagging is used when you have multiple VLAN switches and a distributed VLAN.
As an example imagine you had devices in the living room connected to a smart switch and devices in a home office connected to a second smart switch.
Now you want some devices in the living room to be on the same VLAN.
Because they are physically connected to two different switches you will need to used tagging.
Because this is more complex I will cover it in its own tutorial at a later date but TP-Link include it as an example here.
For this tutorial we will take an example of a single switch with no tagging and configure two VLANs (main and guest ) with both VLANs able to connect to the Internet.
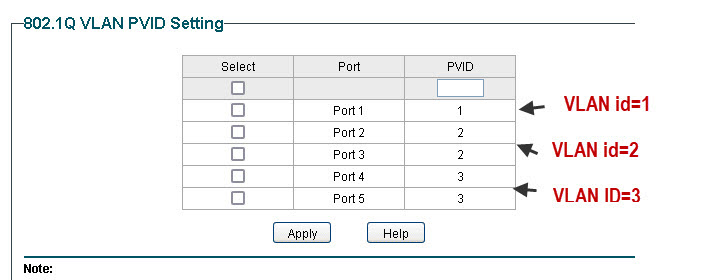
The following schematic is a modified schematic taken from the TP-Link site here.
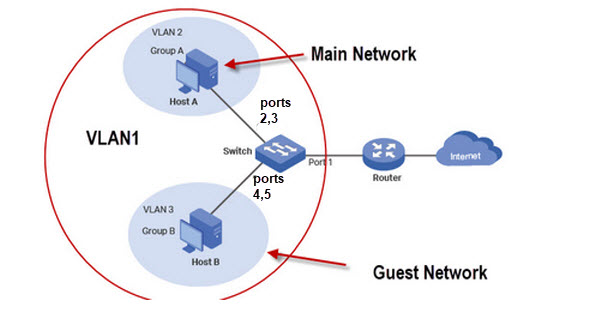
Although we have only two networks (guest and main) we require 3 VLANs.
As port 1 connects the switch to the router all ports need access to this port and so we configure VLAN1 as the default to include all ports.
VLAN2 is the main network and we will use ports 1,2 and 3. VLAN3 is the guest network with ports 1,4 and 5.
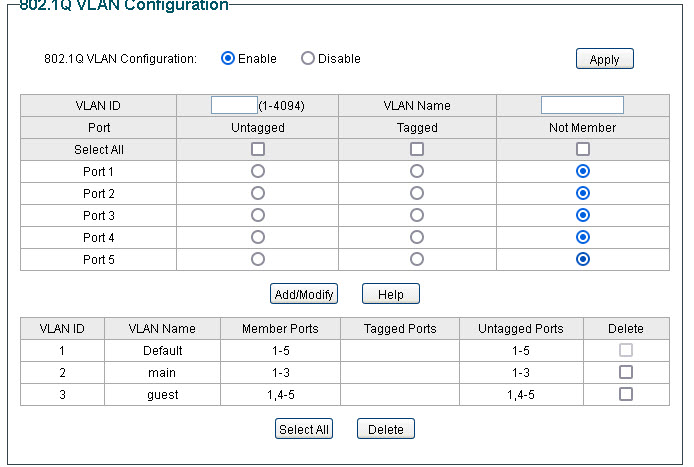
Now the not very obvious configuration is the PVID (port VLAN ID) settings which must be done for this to work the PVID must match the VLAN ID.
TP-Link Router Configuration for Guest Network
This is the configuration I use for a guest network on my home network.
My TP-Link Router also supports VLANS, and so I connect my guest network which is in the basement to LAN1 (port1) and assign it to its own VLAN.
There is no option to assign a Wan Interface as it is automatically allowed.
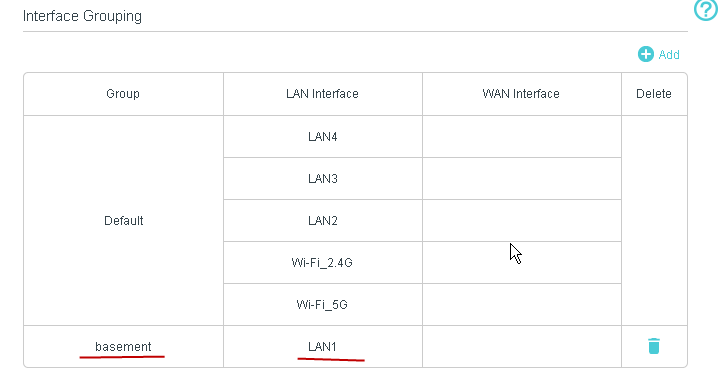
This is a schematic of my home network using the TP-link router..
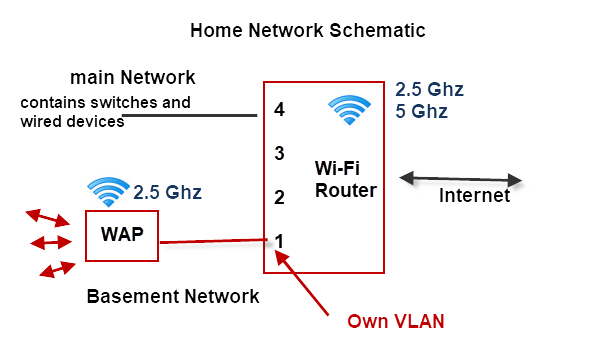
Notes:
- The Wi-Fi router is on the main network VLAN.
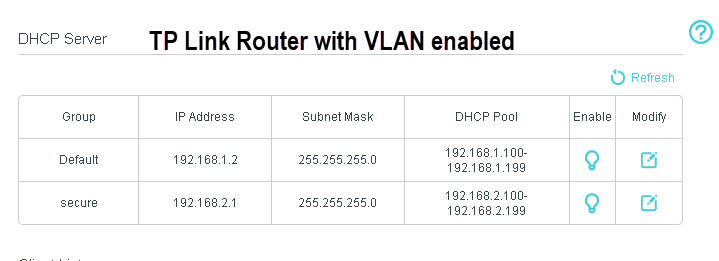
- The Router assigns a different subnet to the second VLAN. The main network uses 192.168.1.0 and the basement VLAN uses 192.168.2.0
- The basement VLAN has its own WAP
The DHCP server on the router is automatically configured to assign addresses on the new subnet as shown below:
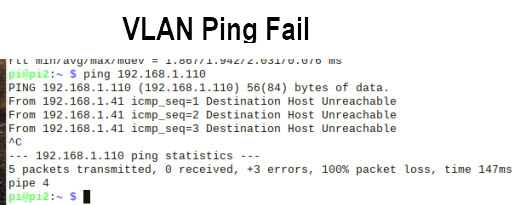
Home Network VLAN Testing
The easiest way of testing is using the ping command.
You should not be able to ping machines on different VLANs.
DHCP server Notes
The DHCP server must be located on a VLAN that is accessible by all other VLANs which usually means it is on the Internet router.
If you want a VLAN to use a separate DHCP server than the one on the router then you can install one on the VLAN without causing a problem to machines on the other VLANs.
However because a VLAN has a DHCP server it doesn’t prevent it from using the central DHCP server, and you cannot guarantee that a client on the VLAN will get the address from the local DHCP server.
Simple Home network Design Example
Example 1
You have lodgers or a guest house and want to isolate guest machines from your main network but give them access to the Internet.
Your router doesn’t support VLANs and guest Wi-Fi doesn’t have the range. You cannot change the router and both the guest and main network need Wi-Fi access
Solution
You will need a VLAN capable switch to split the network. You will also need to Wireless access points and shouldn’t use the WI-Fi provided by the main router.
A schematic is show below:
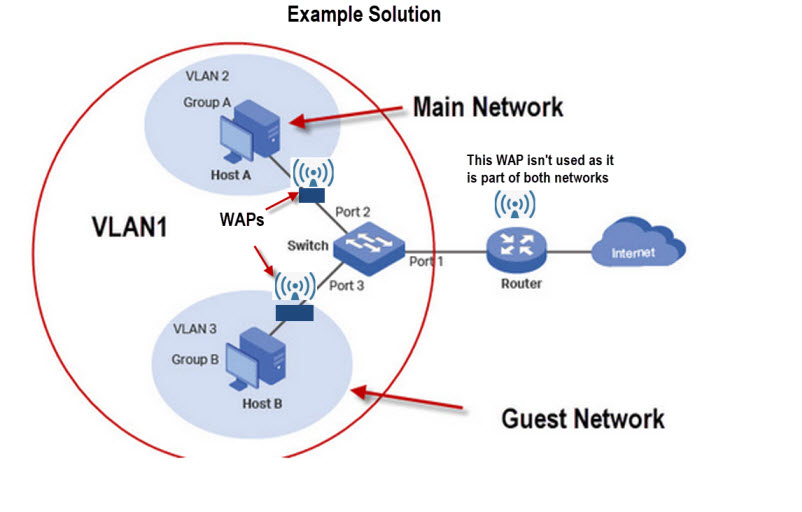
The above solution can be achieved using 802.1Q VLAN or MTU VLAN modes on the switch.
Quick Questions
Referring to the schematic for solution 1 above.
Q1- If you connect a device to the main Wi-Fi router using Wi-Fi will you be able to ping a devices on the guest and main network? Yes or No.
Q2. Will a device on the main network be able to ping a device on the main network? Yes or No.
Q3: The main router also has 3 spare Ethernet ports. Can you use them?
Q4 On what device do you think the DHCP server is located?
Answers
A1 Yes
A2 Yes
A3 If you do it will not be secure.
A4 The main router
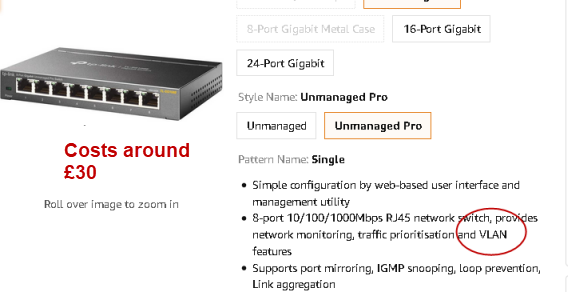
Switches With VLAN Support
Usually if the switch is labelled as a smart switch or managed switch it will have VLAN support but you should read the description to be sure.
Below is screen shot from Amazon of a TP-link switch (£30) that supports VLANs.
VLANS vs Subnets
VLANs work on switches whereas to implement subnets you need a router.
A routed network is more difficult to setup than a switched network.
However a routed network does create separate broadcast domains while a switched network doesn’t unles you use VLANs.
The general rule is switch when you can and route when you must.
See Home Network Subnet Mask Explained
Summary
The main benefit of VLANs is that they provide an excellent and low cost method of greatly improving you home network security.
Although they also reduce broadcast traffic this is not usually necessary on a home network.
However if you have several hundred devices then this is a distinct advantage and so VLANs should be used.
Terms Used in this Tutorial
broadcast traffic– traffic that is end to all hosts(devices) on an network. Many network services rely on this type of traffic e.g ARP and DHCP.
ARP– protocol used to resolve obtain the MAC address of a device using and iP address.
DHCP– Protocol for obtaining an IP address. See Understanding DHCP on Home Networks
Related Tutorials and Resources
- How To Segment A Small LAN Using Tagged VLANs
- VLAN How To: Segmenting a small LAN
- Private VLANs -Wiki
- Basic Home Networking course
- A Beginners Guide to Proxy Servers and VPNs
- How to Create a guest Network
- How to Isolate Your Home Network from Your Smart Home Network
I got the tp-link but noticed there is no mdns traffic on the network at all, is there something I am missing ?
Not quite sure of the connection between mdns and vlans can you explain more.
Rgds
Steve
Hello Steve and thank you so much for this guide.
I have recently bought a QNAP NAS and I am wanting to create 2 VLANS, one for each network card on my PC.
My thoughts are to have one VLAN for constant syncing / backup and the second for general internet use.
It’s a bit more complicated than this as I have more than just these 2 machines but am I on the right track please?
Can I have the same PC and the same NAS communicating on 2 different VLANS (via different network cards) at the same time?
I wouldn’t use a VLAN for this . Having two network cards usually implies to ip subnets so the NAS is on one subnet and for that you don’t actually need a router provided only the PC and NAS device want to talk.You will almost certainly need a second switch to connect the two together.
However I think you might be making it two complex but I don’t know your exact requirements. Take a look here
https://hypertecdirect.com/knowledge-base/nas-vs-san/
there are two diagrams which show typical layout the first one is NAS and the second SAN.
Rgds
Steve
Hi Steve,
What TP-Link router are you using that supports the VLANS please ?
The tutorial use an tp archer VR400 v2
rgds
steve
Hi Steve,
i am just looking through the manual for that product and on the simulator but I dont see a interface grouping, do you have a particular firmware on that I think the router sim and manual is for v3 ?
regrads
Try
Advanced>network>interface grouping
rgds
steve
I have checked details on TP Link Website about “TP Link TL-SG108E V6”
Step A
ISP Router’s WiFi Function will be Disabled. It’s WiFi will not be used.
ISP WiFi Router — To — > Port 1 of TP Link TL-SG108E V6
Step B
Ethernet Connected Computers are Connected to Port 2, Port 3 and Port 4 of TP Link TL-SG108E V6
Computer 1 — > Port 2 (of TP Link TL-SG108E V6)
Computer 2 — > Port 3 (of TP Link TL-SG108E V6)
Computer 3 –> Port 4 (of TP Link TL-SG108E V6)
Step C
Separate WiFi Router (TP Link Archer C6 or something Normal WiFi Router) is attached to Port 5.
Step D
Keep port 1, 2, 3, 4 and 5 in VLAN 1. (By default, all ports belong to VLAN 1.)
Create VLAN 2. Add port 1, 2, 3 and 4 to VLAN 2.
Create VLAN 3. Add port 1 and 5 to VLAN 3.
My understanding – and – Expectation
The Computers / Laptops connected to WiFi Router at Port 5, will be able to Access Internet.
But Computers / Laptop connected to WiFi Router at Port 5, will not be able to communicate with ‘Wired Ethernet Connected Computers” at Port 2, Port 3 and Port 4.
Similarly, ‘Wired Ethernet Connected Computers” at Port 2, Port 3 and Port 4. will not be able to communicate with Computers / Laptop connected to WiFi Router at Port 5.
‘Wired Ethernet Connected Computers” at Port 2, Port 3 and Port 4 will be able to get internet access, via Port 1
Whether my Understanding is Correct?
Please Advise
Whether I can get the necessary results from TP Link TL-SG108E V6? Because it is a Managed Switch?
It looks correct for 802.1Q VLAN mode. You also need to set the vlan id as per the tutorial.
rgds
steve
Hello,
I currently have a TP-Link AV1000 powerline wifi extender and just use my Virgin Superhub as my router. I am thinking about buying a dedicated router to setup up VLANs to separate my main devices and IOT. Will the wifi extender have any particular bearing on this?
Many thanks!
For the IOT devices you need another wireless AP that is connected to a Vlan switch as in the multi tenant example.
you connect the existing network to one port of the switch and the IOT network to another port and then the common port connects to the router.
You will have two separate Wi-Fi networks. It is important that your existing network connects to the VLAN switch.
The tp link managed switch is about £20.
Rgds
Steve
Great article. One question though, what TP-link ‘VLAN aware’ router are you using?
From the research I’ve been doing to setup separate networks with my managed switch, most consumer grade routers do not actually appear to be VLAN aware so it’s not that easy even if you have a managed switch as most peoples router do not recognise the tagging.
Thanks
It was a tplink vr400. I didn’t test tagging on it.
rgds
Steve
ok but even without tagging you say above “My TPlink Router also supports VLANS, and so I connect my guest network which is in the basement to LAN1 (port1) and assign it to its own VLAN.”
When I look at the specs on the TP-Link website for the VR400 it doesn’t show support for IEEE 802.1Q. I can’t see how this router is VLAN aware or allows you to assign them even without tagging. I understand it has guest network though but I’m looking to implement VLAN’s using consumer-grade hardware and I can’t see many options with routers.
I’ll most likely go with 2 WAP’s on a Managed switch given it doesn’t seem an option to use a router as you’ve used above (unless I purchase something like a Draytek.)
Maybe I’m misunderstanding what you’ve done in the example above?
Hi
The setting is under interface grouping. I will email you a screen snot
rgds
steve
Is there a way of getting network segmentation for wifi devices via 1 wifi ap/toute? Like
Modem -> router -> WiFi AP
If the router supports VLANs, is it possible to group eg like this:
– iot devices (that connect to network via WiFi) into one vlan
– business devices (laptops, printer etc) into another VLAN
– kids devices into yet another
– and finally a guest network (where devices can not see each other)?
Note: one router and one wifi AP!
Assuming that the wi-fi AP is a separate device to the router then almost. You need to configure the router with 4 vlans each vlan would support the relevant devices.
The guest network is the strange one as it is usually provided by Wi-fi so it would need another wi-fi AP
Rgds
Steve
Is there any way to setup a VLAN so that I have my internal network 192.*.*.* and on one connected port from the switch (eg port 5) configured with a seperate non routable ip range? eg 172.*.*.*?
Switches don’t understand IP addresses. Even tough they are on the same physical network devices on 172 think that that are on a different network than those on 192.
The addresses on 172 would need to be manually assigned. In this scenario I would look at adding a router.
Is there a reason why you use 172. address range?
By non routable do you want to block access to the Internet for devices on 172. network?
Rgds
Steve
Excellent guide. It helped me realize that I can use MTU instead of playing with tagging. I would however still like to understand the tagging. Where is run into a trouble is following the visual with the text. The text has different ports than the example. Is it me reading it wrong please?
“Although we have only two networks (guest and main) we require 3 VLANs.
As port 1 connects the switch to the router all ports need access to this port and so we configure VLAN1 as the default to include all ports.
VLAN2 is the main network and we will use ports 1,2 and 3. VLAN3 is the guest network with ports 1,4 and 5.”
No my mistake I’ve updated the diagram and hopefully it makes more sense now.
Rgds
Steve
Hi Steve, you have provided some very useful and clear information, which has helped me with a network problem I am working on. Thank you very much.
Regards
Glenn
No problem glad to have helped
Rgds
Steve
Good article. However, I would be very suspect of TP-Link networking equipment. TP-Link is a Chinese based company. Swim at your own risk.
Thank you for the write-up. I suspect you might have typo in question 2 at the end (“Will a device on the main network be able to ping a device on the main network? Yes or No.”) I believe the answer to that question is “YES” (not “NO”). However a ping from main to guest will not succeed.
Tks for spotting that I have corrected it.
Rgds
Steve
Hello Steve,
Many thanks for a fine website and great information.
Under ‘implementing examples 1 and 2’ you have a typo under the diagram – they are both labelled “VLAN 1” when the second is supposed to be VLAN 2.
Tks for that I have updated the diagram
rgds
Steve
Hi Steve,
Thank you for this wonderful explanation. I do have a TP-link router as well.
My objective is to create a VLAN for a home lab and seperate it from my main network (192.168.1.1/24). I have configured the interface grouping and enabled the group isolation with my home lab’s network (192.168.2.1/24) on LAN1 interface.
I’m hosting an ESXi server on 192.168.2.2 and I want to be able to access the ESXi management portal from a dedicated deivce on my main network. Is there a way to do this on this router?
Thank you,
Oliver
Hi
Can you use the ask steve page and send me a diagram.
Tks
Steve
Hi, I have a GS116Ev2 switch, trunked to pfSense and also unifi AP. Need to know why DHCPDISCOVER broadcasts are being sent to two of my four VLANs and not just one VLAN that the discover came from. Seems like the switch is sending out two two VLANs. Any one have any ideas? Thank you
hi i’ve followed this through and can’t get it to work at all. I have two vlans 1 and 10 on an hpv1910 48g switch, and i’m using a virginmedia superhub for access. I’ve set both vlans to have a common physical port as a hybrid port that connects by cable directly to the superhub. each vlan has been set to have an ip address , respectively 192.168.0.2 for vlan 1 and 192.168.1.1 for vlan 10. The superhub is the default gateway at 192.168.0.1 . at this point, any clients plugged into vlan 1 by default works fine with full access to the internet and each other. No access to clients in vlan10 , as expected – all good. However, clients in vlan 10 cannot connect to the internet at all. From what you have said above this should just start working but it doesn’t -what could I be doing wrong? is this because the superhub from virginmedia is not vlan aware in any shape way or form and is what i’m trying to achieve effectively impossible?
Hi
Not sure can you use the ask steve page to contact me and then send me a quick diagram of the setup and also a screen shot of the switch.
https://stevessmarthomeguide.com/ask-steve/
Rgds
Steve
Hi,
I am trying to setup a home network that I can do the following:
1. Main network
2. Kids network ( guest network) with parental control
3. Vlan – for smart devices (security reason)
4. Cottage network- for guests
Question:. All the smart devices require wifi access. How does vlan utilize the wifi network? How do I ensure the security ?
If I implemented what you wrote above. Will it accomplish my goal of 4 networks that can be parental controlled separately?
Yes most routers offer guest network ability which is for guests not the kids and would be Wi-Fi only. The parental control for the kids can be done on the device address rather than the network address.
Hi there,
I’m hoping you can help me.
My setup:
I have the following devices as part of my network:
2x TP Link access points (EAP225 and EAP255)
1x Virgin media superhub / router – internet access
1x 16 port TP link unmanaged switch
1x 8 port TP link unmanaged switch
1x 5 port managed switch (TP link SG105E)
On the WiFi access points, I configured them to broadcast three WiFi networks:
IoT (for all my IoT devices)
Guest (for guests)
Home network (everything else that doesn’t fall into the two above)
My requirement:
I have a few devices plugged into both the 8 port and 16 port switches and I’m happy for them to be on ‘Home network’. The other IoT devices and guests connect in via the APs and I would like for them to be separate VLANs.
The issue:
I just want to set up the VLANs on the switch and bind the WiFi networks on the APs to those VLANs (i.e. VLAN ID 2 = Iot, VLAN ID 3 = guest, VLAN ID 1,4,5 = home network).
I can’t figure out how to do this using the web based configuration on the SG105E – getting confused between MTU, port based, 801.2q etc..)
Can you help?
Hi
Can you use the ask steve page and send me a sketch of the setup.
Rgds
Steve
This is great. I wanted to know why and how to utilize VLAN in my home network. I just purchased a refurbished Cisco 3750 and want to put it my network. I am assuming that my modem/router from Spectrum/ATT/Comcast etc. would plug into on port on the switch.
So I can configure on port on the switch to be available to many VLANs?